Go provision yourself.
Onboarding users in a passwordless world.
Onboarding new users to an Identity platform (iDp) shouldn’t be challenging. As the first fully Passkey-driven Identity and Access Management platform, we can rethink the onboarding experience. While transitioning to a completely “passwordless” environment may seem daunting, it’s actually straightforward and can be streamlined for ease of use.
At Key9, we have a concept called "provisioned users." This is an innovative approach to setting up new users in a highly secure manner. To illustrate, let’s consider an example company that uses Key9 as its identity provider (iDp) and YubiKeys to secure its network and applications.
As a Key9 administrator, you can have a Yubikey shipped directly to the user’s location and send a registration “magic link.” While this process works, it requires users to undertake quite a bit of effort to set up their own Yubikey, which can be confusing, especially for new users.
Ultimately, passwordless technology should simplify the experience, not complicate it further.
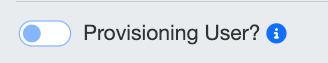
At Key9, an alternative method is available. When the administrator sets up a new user, they can enable the “Provisioning user?” option.
This informs Key9 that you wish to bypass the standard verification processes. While this may initially seem less secure, it actually isn't.
When this option is enabled, the administrator can set up the user as usual by assigning privileges and groups. However, the administrator also has the option to pre-configure the Yubikey.
For instance, after entering all the user’s information, the administrator can insert a new Yubikey into their workstation. At that point, the administrator can assign a PIN to the Yubikey and generate a Passkey for the user. Don’t worry; later, we’ll discuss how the PIN plays into the secure transfer.
Key9 will manage the public key as usual, while the YubiKey will securely store the private key. The design of YubiKeys ensures that even administrators cannot access the private key, providing an additional layer of protection.
After the user has been created and assigned a pre-generated Passkey stored on the Yubikey, the physical key must be transferred to the user.
In certain situations, handing over a Yubikey to a user can be as simple as meeting them in person and providing the PIN. This process is reminiscent of the old "key signing parties." The idea is that when you are face-to-face with someone, you can be confident that the Yubikey has been received by the right person.
In other situations, this may not hold true. This is where we can use the PIN code to help facilitate the transfer.
Imagine a situation where a user is in a different city or country. In this case, the administrator would mail the physical key to the user, along with a note advising them to contact the administrator upon receiving the key. Importantly, the administrator would not include the PIN for that key in the package. Instead, the PIN code would be communicated through a separate, secure method (out-of-bands).
The idea is that if the key is intercepted by someone other than the intended user, the PIN serves as a safeguard to prevent unauthorized access. By default, YubiKeys allow up to eight attempts to enter the correct PIN. If the correct PIN is not entered after these attempts, the FIDO2 applications will block further access, and the key must be reset.
Additionally, after every third failed attempt in a row, the YubiKey must be physically removed and reinserted into the device. This design helps prevent brute-force attacks on the physical key.
Once the user successfully receives their Yubikey, they should notify the administrator. The administrator will then use a pre-established communication method to relay the PIN code to the Yubikey.
For instance, if the user calls the administrator to request the Yubikey PIN, the administrator cannot provide it during that call. Instead, they must hang up and call back using a predetermined phone number to transfer the PIN securely. This prevents social engineering to gaining access to the PIN number.
This is a simple example. An administrator can share the PIN with the user in several ways. For instance, they could use encrypted email or a predetermined instant messaging service like Signal.
The final issue to address is the possibility that the administrator may know all the YubiKey PINs. Fortunately, this can be easily resolved. Users can change their PINs using the built-in security key tools in Windows 11 or the security key management tools available in web browsers like Google Chrome. This means users can update their PINs without installing any third-party software.
In this example, we’re using YubiKeys as a reference, but any FIDO2 hardware token will work just as well. You can envision this as an “onboarding” process for company laptops. The main idea is to pre-register a Passkey for each computer before shipping it out.
I’ve made a short video to show you how the process works. You can watch it on Youtube below:
Passwordless technology is essential; it not only streamlines the onboarding process for new users but also significantly strengthens security.